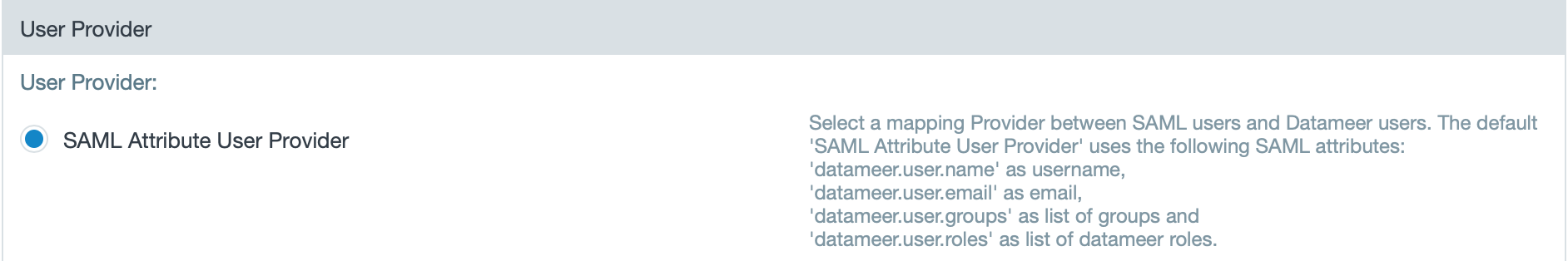
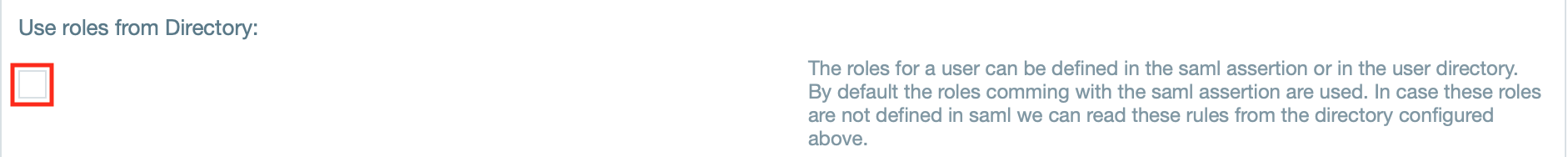
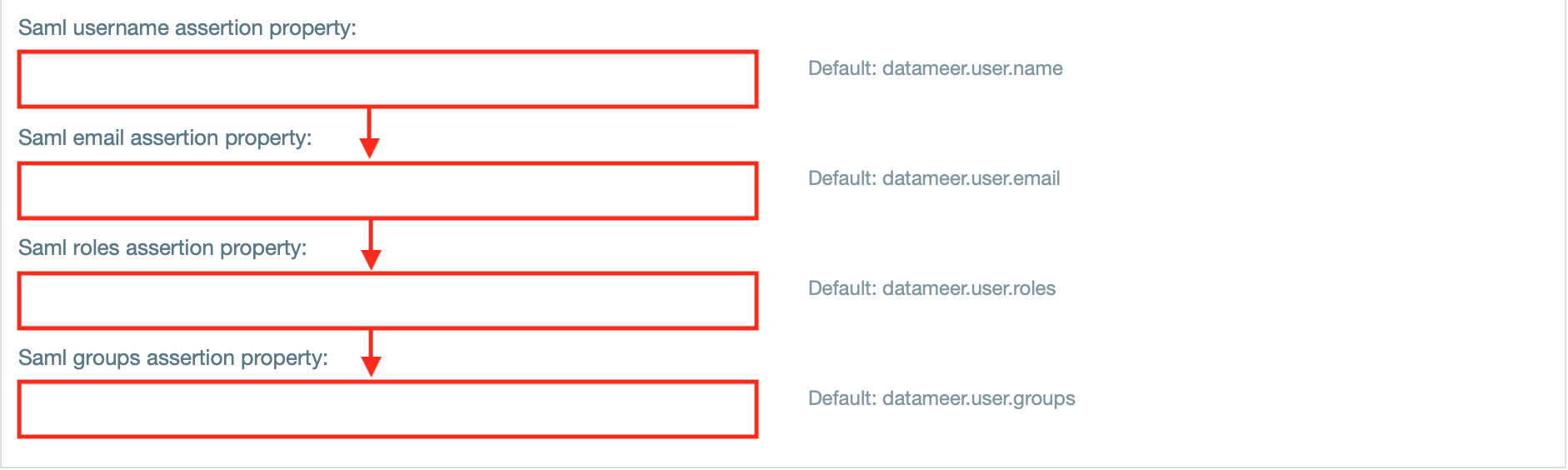
Security Assertion Markup Language (SAML) allows users exchange authorization data between different parties, in particular, between an identity provider and a service provider. The Datameer X SAML Authenticator is designed to allow Datameer X to act as a Service Provider with a SAML SSO (Single Sign On) environment. This means that authentication and identity management happen externally to the Datameer X instance. These services are provided by an Identity Provider which authenticates end users and issue assertions containing subject and session information along with arbitrary attributes about the user. The SAML Authenticator plug-in exposes some extension points to allow customers to provide the appropriate Datameer X user details (group memberships, roles, username, email) based on the incoming assertion. |
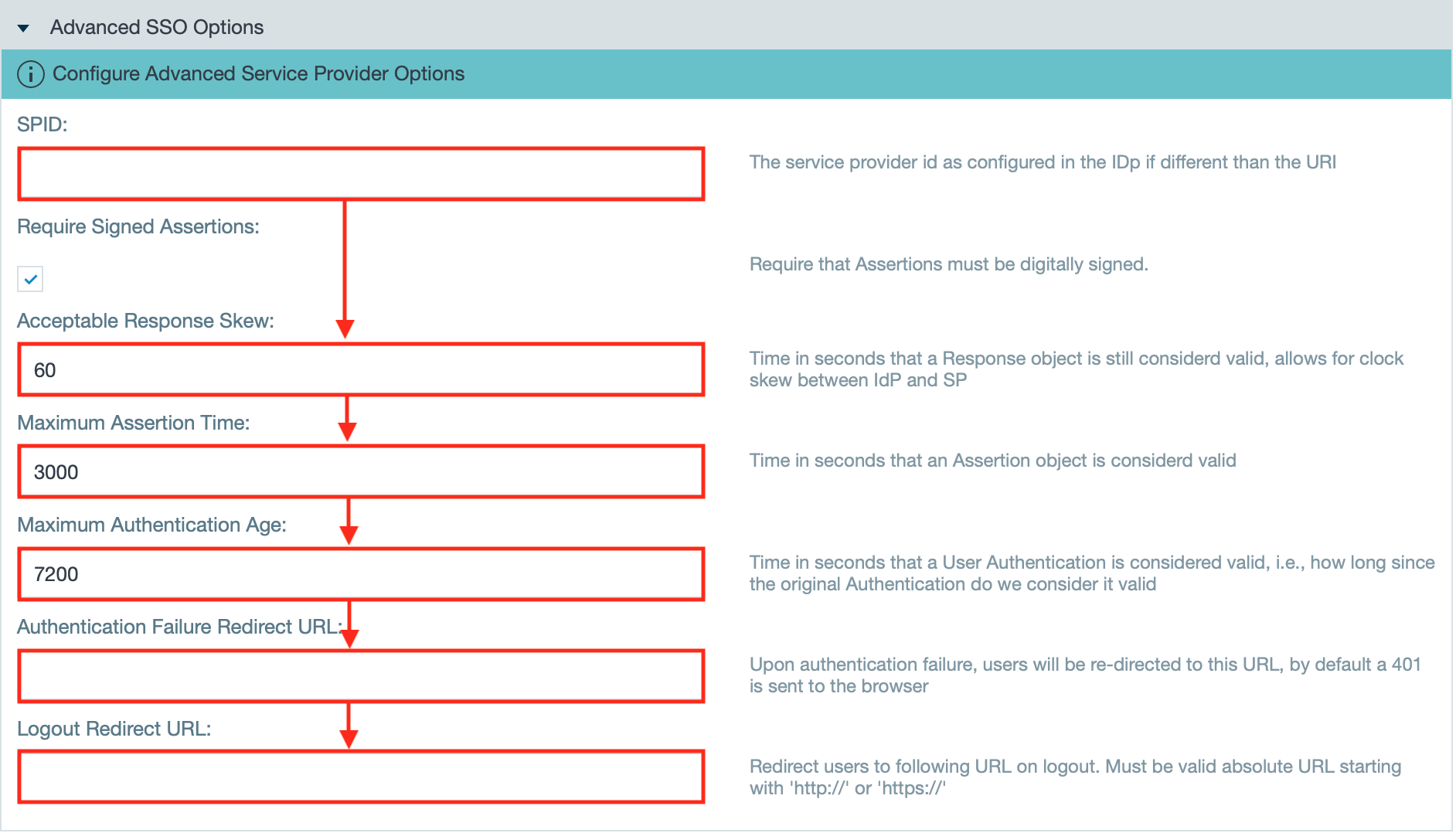
The SAML authenticator requires an authentication repository that resolves the available users to your Datameer X instance. The SAML authentication repository should have a signed assertion signature, and the clocks between the authentication side and the Datameer X side need to be in sync. The authentication side sends an expiration time to their response token. If the clocks are not in sync, the token can be expired or invalid. |
Note that you need to implement SAML SSO SDK Extensions to configure SAML authentication. |
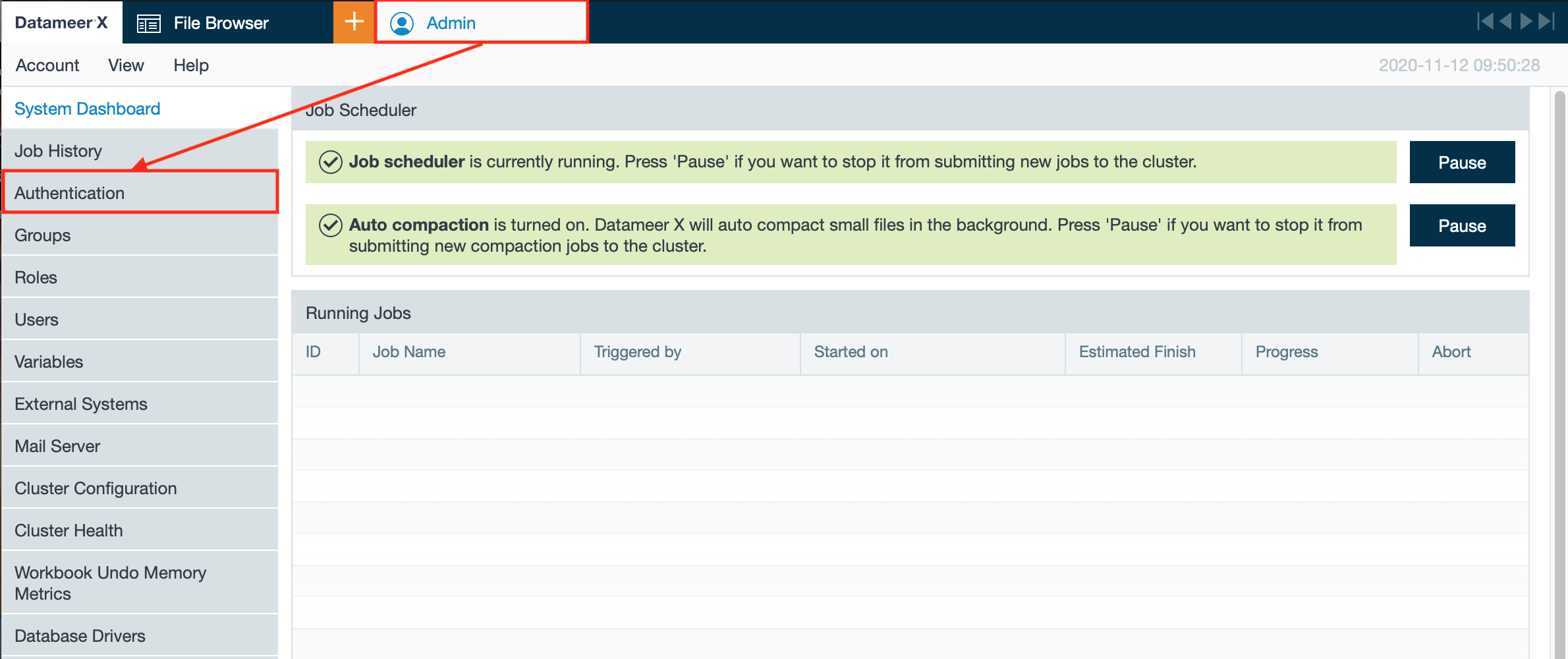
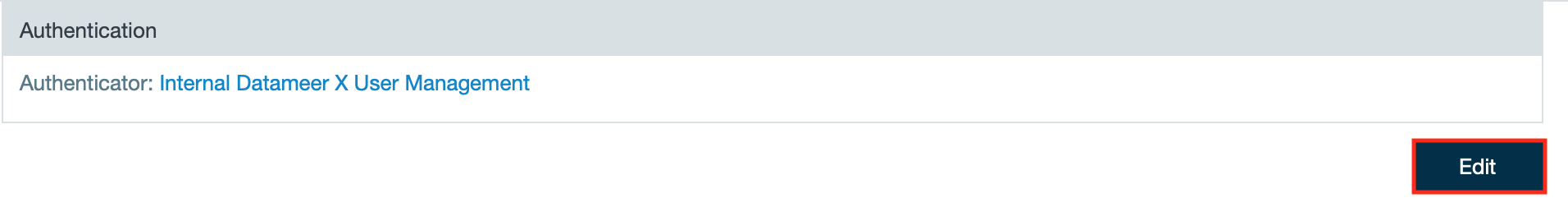
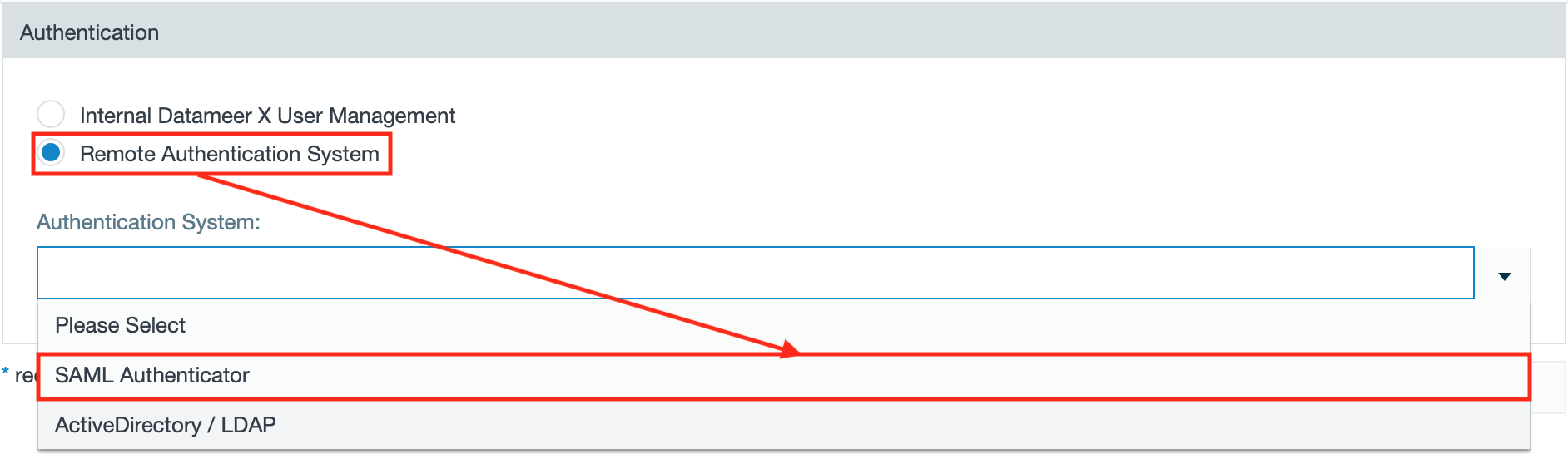
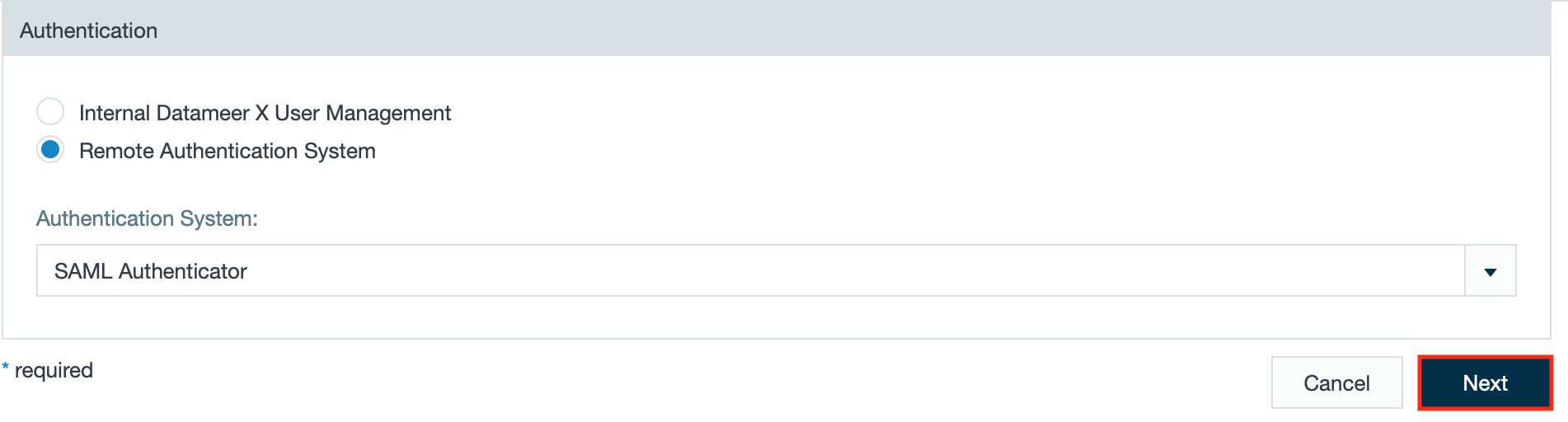
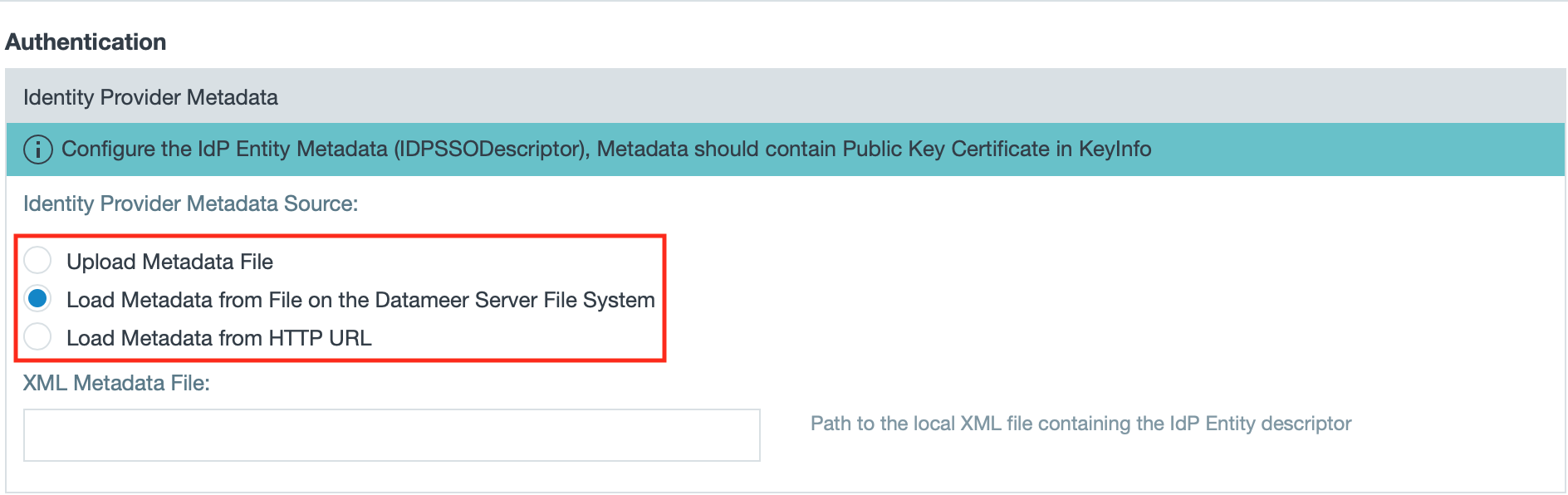
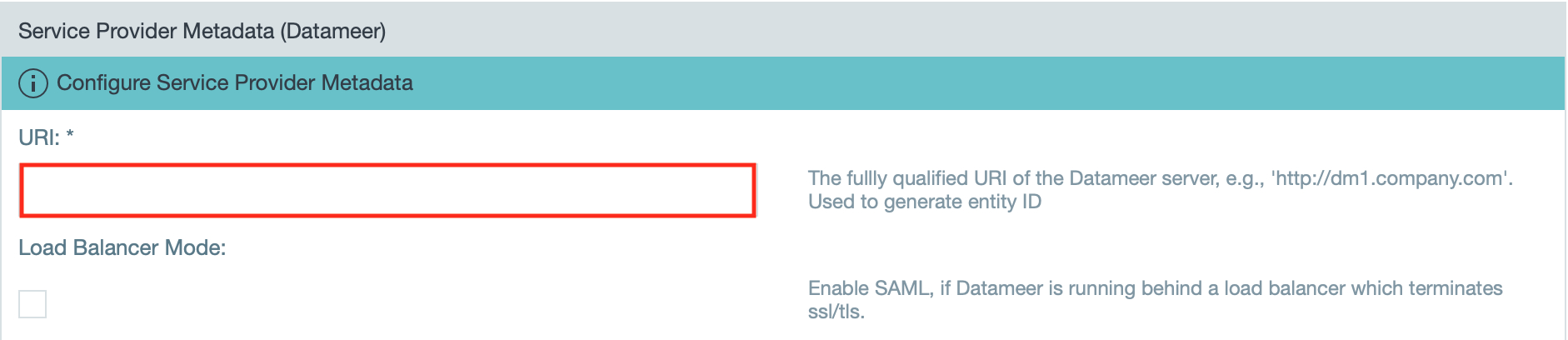
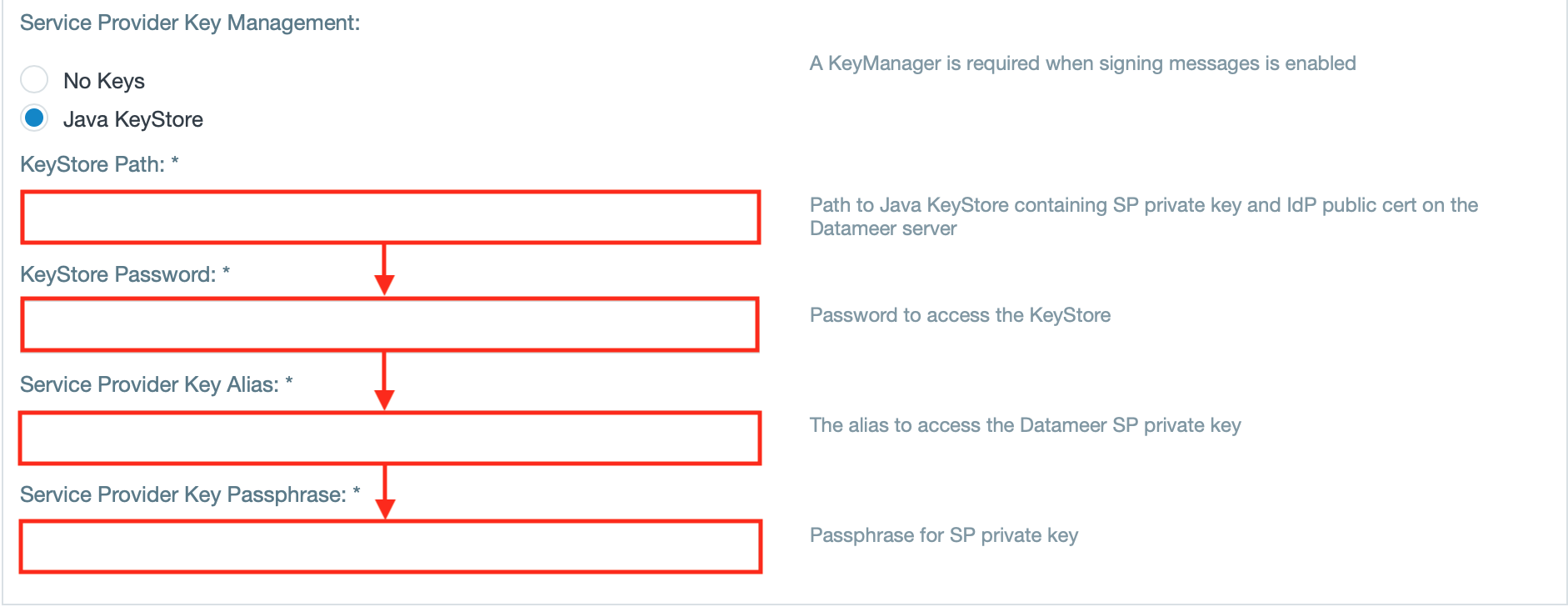
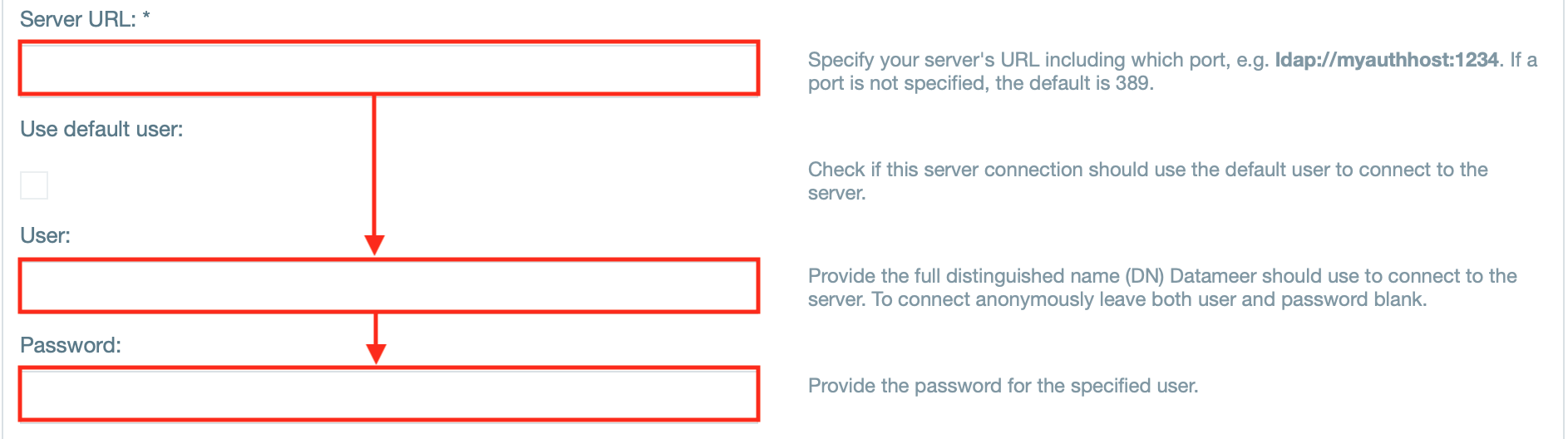
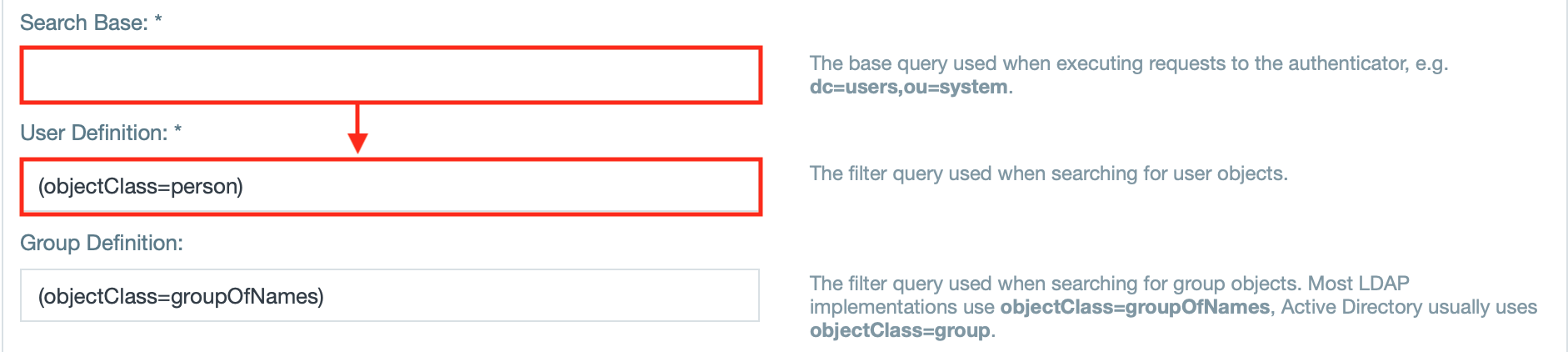
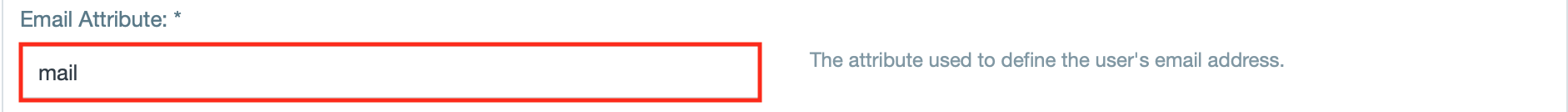
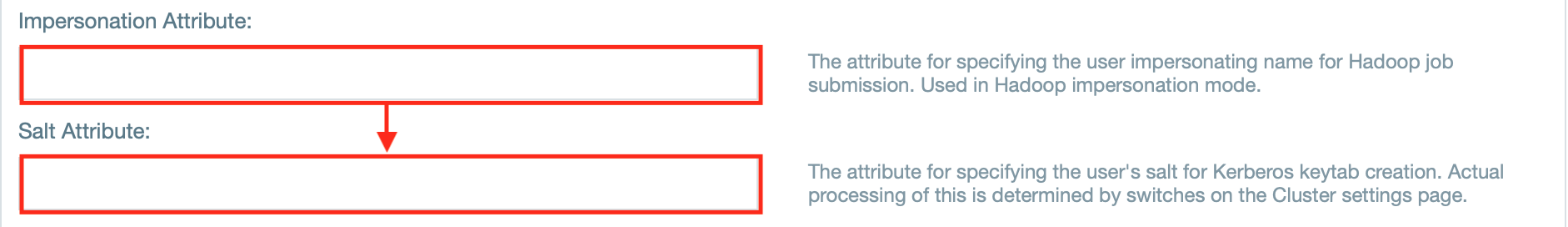
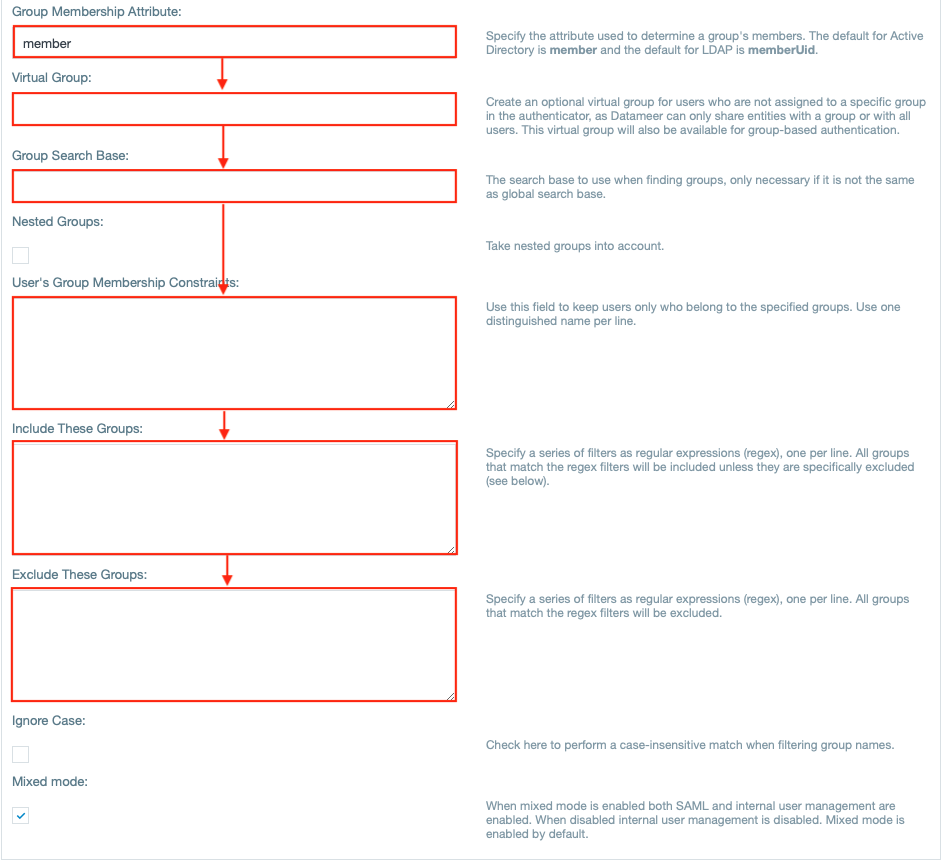
To configure a SAML authentication:





When setting up Okta app integration, an additional configuration within Okta is necessary.
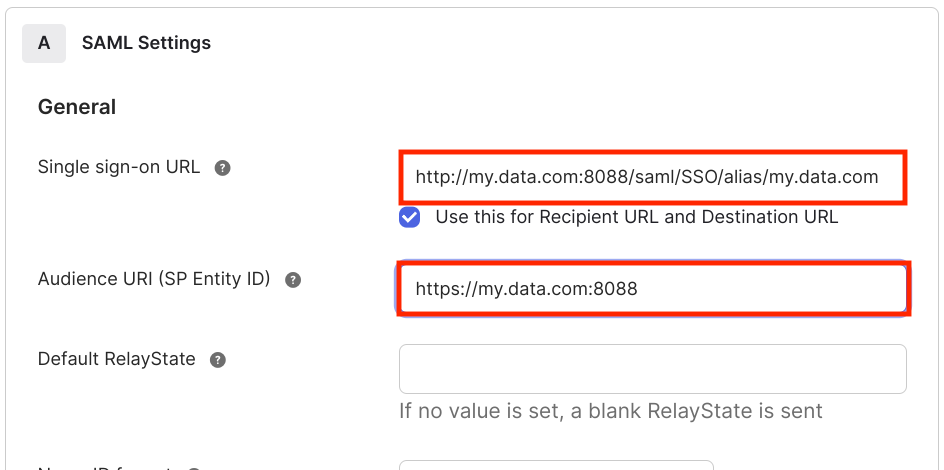
Open the SAML settings in your Okta app and enter a value for "Single sign-on URL" and "Audience URI".
The full qualified URI gets the suffix /saml/SSO/alias/my.data.com:
To enable debugging of SAML edit the 'log4j-production.properties' file and add the following:
log4j.category.com.<package_name>=ERROR #openSAML log4j.category.org.opensaml=ERROR log4j.category.org.springframework.security.saml=ERROR log4j.category.org.springframework.security.web.authentication=ERROR |